SELF - SPRX
| This article is marked for rewrite/restructuring in proper wiki format. You can help PS3 Developer wiki by editing it. |
SELF stands for Signed Executable and Linkable Format. It is the format used by the executables on the PS3 and PS Vita.
Introduction
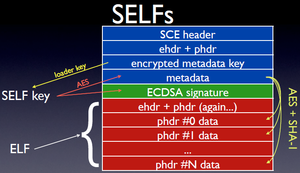
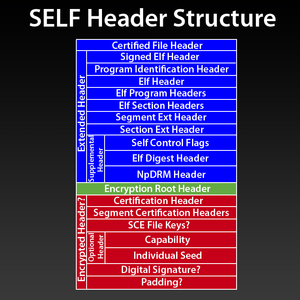
It consists of an extended header followed by the encapsulated ELF file. ELF segments can be compressed using gzip. System and NPDRM SELFs are encrypted and signed and are decrypted in memory. ELF sections might be encrypted using AES CTR (maybe more algos?) and signed using ECDSA + HMAC-SHA1. It has a specific header here called Extended header where it stores all the parameters for this process.
- Extended Header
It consist on information regarding the structure and offsets of the self. The first part is in plaintext until you reach Metadata Info.
- Metadata Info
Metadata Info is itself under AES 256 CBC. This part contains KEY + IV to further decrypt the header using AES 128 CTR.
- Metadata
The metadata header, Metadata Section Headers, Section Hash, Capabilities and Signature are under this AES 128 CTR layer and is decrypted with the key above.
- Metadata Header
Metadata header contains the info required to authenticate the header and the structure of the metadata. The signature is ECDSA of the SHA1 hash of the self file starting at 0x0 and ending at 0x0+signatureInputLength
- Data Sections
The data sections might be encrypted using AES 128 CTR and/or compressed. HMAC-SHA1 is used to authenticate they have not been modified.
Cryptography
Here is a small summary on how the self cryptography works.
Basically here are the steps being involved by the loaders:
Loaders all have a static key and iv called respectively erk and riv, those are keys for the first decryption step which are used to decrypt the very first 0x40 bytes of the self's metadata using AES256CBC
Then the result is used as a key and iv to decrypt the rest of the metadata using AESCTR, finally the decrypted metadata contains the keys and iv for each data sections which are still decrypted through AES128CTR. This security model is based on the fact that the first 0x40 bytes of the self's metadata once decrypted by the static AES256CBC key in the loader should never be the same from one binary to the other. The same goes for any other value used as an AES128CTR key or iv.
Loaders are also involved with inflating the binaries using zlib.
The self authenticity is based on other independent steps, HMAC-SHA1 of the data sections and ECDSA for the actual signature in the header.
Short references
More indepth Online course about encryption in generic (also AES/ECDSA): Lecture Notes on Computer and Network Security by Avinash Kak
File Format
Notes:
- Warning: PS3 uses big endian, PSVita uses little endian.
- Encapsulated ELF header fields are useless (only the EI_CLASS EI_DATA and EI_VERSION fields are checked)
PS3 early type 3 SELFs
SDK 0.60: No sce version and digest SDK 0.8X: No sce version, with 0x30 digest SDK 009X: With sce version and 0x40 digest (scetool produces this type)
Extended Header
Extended Header offsets are relative to Certified File start.
Struct
typedef struct { // Size is 0x50 bytes
uint64_t ext_hdr_version;
uint64_t program_identification_hdr_offset;
uint64_t ehdr_offset;
uint64_t phdr_offset;
uint64_t shdr_offset;
uint64_t section_info_offset;
uint64_t sceversion_offset;
uint64_t supplemental_hdr_offset;
uint64_t supplemental_hdr_size;
uint64_t padding;
} __attribute__((packed)) ext_hdr;
Table
| field | offset | type | notes |
|---|---|---|---|
| Extended Header version | 0x0 | u64 | 3 for PS3, 4 for PSVita |
| Program Identification Header offset | 0x8 | u64 | Offset to Program Identification Header. |
| ELF Header offset | 0x10 | u64 | Offset to ELF header. |
| Program Header offset | 0x18 | u64 | Offset to Program Header. |
| Segments Header offset | 0x20 | u64 | Offset to Section Header. |
| Section Info offset | 0x28 | u64 | Offset to Section Info. A table which maps phdr entries to the actual offset/size within the encrypted CF.
Because CF can be compressed, they might not match the values listed within the ELF. |
| sceversion offset | 0x30 | u64 | Offset to a header which contains some version information, including an offset to the .sceversion section of the encrypted elf. |
| Supplemental Header offset | 0x38 | u64 | Several information containers. |
| Supplemental Header size | 0x40 | u64 | |
| Padding | 0x48 | u64 |
Comments
The real ELF data is located after the extended header (see header size). It is encrypted, unless attribute is 0x8000. unfself works by cutting the SCE header from the (fake)SELF and if needed decompressing sections.
Program Identification Header
Temp name was App Info. Official name is Program Identification Header.
Struct
typedef struct {
uint64_t program_authority_id;
uint32_t program_vendor_id;
uint32_t program_type;
uint64_t program_sceversion;
uint64_t padding;
} __attribute__((packed)) program_identification_header;
Table
| field | offset | type | notes | example |
|---|---|---|---|---|
| program_authority_id | 0x00 | u64 | AuthorityId authority_id | ex: 21 00 00 10 1C CA 01 30 |
| program_vendor_id | 0x08 | u32 | See VendorId vendor_id | ex: 00 00 00 00 |
| program_type | 0x0C | u32 | See Program Type | ex: 08 00 00 00 |
| program_sceversion | 0x10 | u64 | ?SDK version or app version? version ex: 01.02 is translated by make_fself.exe to 02 01 00 00 | ex: 0x0000036000000000 (3.600.011), 0x0000009450000000 (0.945.040) |
| padding | 0x18 | u64 | Padding | 00 00 00 00 00 00 00 00 |
Comments
Aligned to 0x10 bytes.
ELF Header
Struct
typedef struct {
uint8_t e_ident[16]; /* ELF identification */
uint16_t e_type; /* object file type */
uint16_t e_machine; /* machine type */
uint32_t e_version; /* object file version */
uint64_t e_entry; /* entry point address */
uint64_t e_phoff; /* program header offset */
uint64_t e_shoff; /* section header offset */
uint16_t e_flags; /* processor-specific flags */
uint32_t e_ehsize; /* ELF header size */
uint16_t e_phentsize; /* size of program header entry */
uint16_t e_phnum; /* number of program header entries */
uint16_t e_shentsize; /* size of section header entry */
uint16_t e_shnum; /* number of section header entries */
uint16_t e_shstrndx; /* section name string table index */
} __attribute__((packed)) ELF;
Comments
See also specifications: ELF Header ELF-64 Object File Format yifanlu specs
Processor specific elf types (e_type):
/* SCE-specific definitions for e_type: */
#define ET_EXEC 0x0002 /* SCE Executable file */
#define ET_SCE_EXEC 0xFE00 /* SCE Executable file */
#define ET_SCE_RELEXEC 0xFE04 /* SCE Relocatable Executable file */
#define ET_SCE_STUBLIB 0xFE0C /* SCE SDK Stubs */
#define ET_SCE_DYNAMIC 0xFE18 /* Unused */
#define ET_SCE_IOPRELEXEC 0xFF80 /* ? */
#define ET_SCE_IOPRELEXEC2 0xFF81 /* ? */
#define ET_SCE_EERELEXEC 0xFF90 /* ? */
#define ET_SCE_EERELEXEC2 0xFF91 /* ? */
#define ET_SCE_PSPRELEXEC 0xFFA0 /* Unused (PSP ELF only) */
#define ET_SCE_PPURELEXEC 0xFFA4 /* Unused (SPU ELF only) */
#define ET_SCE_ARMRELEXEC 0xFFA5 /* SCE Prototype Relocatable Executable file */
#define ET_SCE_PSPOVERLAY 0xFFA8 /* ? */
EI_OSABI:
- ELFOSABI_CELL_LV2 = 0x66
ELF Program Headers
Struct
typedef struct {
uint32_t p_type; /* type of segment */
uint32_t p_flags; /* segment attributes */
uint64_t p_offset; /* offset in file */
uint64_t p_vaddr; /* virtual address in memory */
uint64_t p_paddr; /* reserved */
uint64_t p_filesz; /* size of segment in file */
uint64_t p_memsz; /* size of segment in memory */
uint64_t p_align; /* alignment of segment */
} __attribute__((packed)) ELF_PHDR;
Comments
See Spec here: ELF Program Headers
Processor specific segment types (p_type):
- PT_SCE_IOPMOD = 0x70000080
- PT_SCE_EEMOD = 0x70000090
- PT_SCE_PSPREL = 0x700000A0
- PT_SCE_PPURELA= 0x700000A4
- PT_SCE_SEGSYM = 0x700000A8
Processor specific segment flags (p_flags):
- PF_SPU_X = 0x00100000
- PF_SPU_W = 0x00200000
- PF_SPU_R = 0x00400000
- PF_RSX_X = 0x01000000
- PF_RSX_W = 0x02000000
- PF_RSX_R = 0x04000000
ELF Section Headers
Struct
typedef struct {
uint32_t sh_name; /* section name */
uint32_t sh_type; /* section type */
uint64_t sh_flags; /* section attributes */
uint64_t sh_addr; /* virtual address in memory */
uint64_t sh_offset; /* offset in file */
uint64_t sh_size; /* size of section */
uint32_t sh_link; /* link to other section */
uint32_t sh_info; /* miscellaneous information */
uint64_t sh_addralign; /* address alignment boundary */
uint64_t sh_entsize; /* size of entries, if section has table */
} __attribute__((packed)) ELF_SHDR;
Comments
Processor specific section types (sh_type):
- SHT_SCE_IOPMOD = 0x70000080
- SHT_SCE_EEMOD = 0x70000090
- SHT_SCE_PSPREL = 0x700000a0
- SHT_SCE_PPURELA = 0x700000a4
Segment Information (program header)
There is one of these entries (Section/Segment Information) for each ELF phdr entry (Program Header) in the ELF file so that the console knows where to decrypt the data from (because it might also be compressed).
Struct
typedef struct {
uint64_t offset;
uint64_t size;
uint32_t compression;
uint32_t unknown;
uint64_t encryption;
} __attribute__((packed)) SECTION_INFO;
Table
| field | offset | type | notes |
|---|---|---|---|
| Offset | 0x00 | u64 | Offset to data |
| Size | 0x08 | u64 | Size of data |
| Compression | 0x10 | u32 | 1 = uncompressed, 2 = compressed |
| Unknown | 0x14 | u32 | Always 0, as far as I know. |
| Encryption | 0x1C | u64 | 1 = encrypted, 2 = unencrypted |
SCE Version Info
Struct
typedef struct {
uint32_t subheader_type; // 1 - sceversion
uint32_t present; // 0 = false, 1 = true
uint32_t size; // ex: 0
uint32_t unknown4;
} __attribute__((packed)) SCEVERSION_INFO;
Data Struct
typedef struct {
uint16 unknown_1;
uint16 unknown_2; // 0x1
uint32 unknown_3;
uint32 unknown_4; // ?Number of sections?
uint32 unknown_5;
////
uint64 offset; // Data offset
uint64 size; // Data size
//// <- these are supposed to be sections
} SCE_VERSION_DATA_30;
Comments
Supplemental Header
Temp name was Control Information. Official name is Supplemental Header.
Struct
typedef struct {
uint32_t type; // 1=PS3 control flags; 2=PS3 ELF digest info; 3=PS3 NPDRM info, 4=PSVita ELF digest info; 5=PSVita NPDRM info; 6=PSVita boot param info; 7=PSVita shared secret info
uint32_t size;
uint64_t next; // 1 if another Supplemental Header element follows else 0
union {
// type 1, 0x30 bytes
struct { // 0x20 bytes of data
uint32_t ctrl_flag1; // [[Control Flags|ctrl_flag]] 0x80000000(all?); 0x40000000(root); 0x20000000(dbg); 0x00000000(normal?)
uint32_t unknown2;
uint32_t unknown3;
uint32_t unknown4;
uint32_t unknown5;
uint32_t unknown6;
uint32_t unknown7; // ex: 0;8;9;0xC
uint32_t unknown8; // ex: 0;1;2;4
} PS3_control_flags;
// type 2, 0x40 bytes
struct { // 0x30 bytes of data
uint8_t constant[0x14]; // same for every PSVita/PS3 SELF, hardcoded in make_fself.exe: 627CB1808AB938E32C8C091708726A579E2586E4
uint8_t elf_digest[0x14]; // on PSVita: SHA-256 of source ELF file, on PS3: SHA-1. Hash F2C552BF716ED24759CBE8A0A9A6DB9965F3811C is blackisted by appldr
uint64_t required_system_version; // filled on Sony auth server, contains decimal PS3_SYSTEM_VER value from PARAM.SFO
} PS3_elf_digest_40;
// type 2, 0x30 bytes
struct { // 0x20 bytes of data
uint8_t constant_or_elf_digest[0x14];
uint8_t padding[0xC];
} PS3_elf_digest_30;
// type 3, 0x90 bytes
struct { // 0x80 bytes of data
uint32_t magic; // 4E 50 44 00 ("NPD.")
uint32_t license_version;
uint32_t drm_type; // [[License Types|license_type]]
uint32_t app_type; // [[App Types|app_type]]
uint8_t content_id[0x30];
uint8_t digest[0x10]; // sha-1 hash of debug self/sprx created with make_fself_npdrm
uint8_t inv_digest[0x10]; // hash_cid_fname
uint8_t xor_digest[0x10]; // hash_cid
uint8_t padding[0x10];
} PS3_npdrm_info;
// type 4, 0x50 bytes
struct { // 0x40 bytes of data
uint8_t constant[0x14]; // same for every PSVita/PS3 SELF, hardcoded in make_fself.exe: 627CB1808AB938E32C8C091708726A579E2586E4
uint8_t elf_digest[0x20]; // on PSVita: SHA-256 of source ELF file, on PS3: SHA-1
uint8_t padding[8];
uint32_t min_required_fw; // ex: 0x363 for 3.63
} PSVita_elf_digest_info;
// type 5, 0x110 bytes
struct { // 0x80 bytes of data
uint32_t magic; // 7F 44 52 4D (".DRM")
uint32_t finalized_flag; // ex: 80 00 00 01
uint32_t drm_type; // [[License Types|license_type]] ex: 2 local, 0xD free with license
uint32_t padding;
uint8_t content_id[0x30];
uint8_t digest[0x10]; // ?sha-1 hash of debug self/sprx created using make_fself_npdrm?
uint8_t padding_78[0x78];
uint8_t hash_signature[0x38]; // unknown hash/signature
} PSVita_npdrm_info;
// type 6, 0x110 bytes
struct { // 0x100 bytes of data
uint32_t is_used; // 0=false, 1=true
uint8_t boot_param[0x9C]; // ex: starting with 02 00 00 00
} PSVita_boot_param_info;
// type 7, 0x50 bytes
struct { // 0x40 bytes of data
uint8_t shared_secret_0[0x10]; // ex: 0x7E7FD126A7B9614940607EE1BF9DDF5E or full of zeroes
uint8_t shared_secret_1[0x10]; // ex: full of zeroes
uint8_t shared_secret_2[0x10]; // ex: full of zeroes
uint8_t shared_secret_3[0x10]; // ex: full of zeroes
} PSVita_shared_secret_info;
};
} __attribute__((packed)) supplemental_header;
Table
Comments
Notes:
- self_control_flags also known as plaintext_capability.
- loader used supplemental_header_table to handle the data.
typedef struct {
uint256_t control_flags; /* self_control_flags */
uint8[0x14] elf_digest; /* sha1 hash of the ELF file */
uint32_t unknown_0; /* seems to be padding */
uint64_t PS3_SYSTEM_VER; /* required_system_vesion, decimal format */
} SUPPLEMENTAL_HEADER_TABLE;
Encryption Root Header
Temp name was Metadata Information. Official name is encryption_root_header.
This is not present in fSELF.
Struct
typedef struct {
uint8_t key[16];
uint8_t key_pad[16];
uint8_t iv[16];
uint8_t iv_pad[16];
} __attribute__((packed)) encryption_root_header;
Comments
Notes:
- The key and ivec fields are encrypted using AES256CBC.
Certification Header
Temp name was Metadata Header. Official name is certification_header.
This is only present if the Encryption Root Header is present.
The Certification Header is located after the Encryption Root Header in the SELF file. It is decrypted using AES128CTR with the key and ivec entries from the Encryption Root Header.
Struct
typedef struct {
uint64_t signatureInputLength;
uint32_t unknown02; // Might be signature algorithm. It always = 1 (ECDSA)
uint32_t sectionCount;
uint32_t keyCount;
uint32_t optHeaderSize;
uint64_t unknown06;
} __attribute__((packed)) certification_header;
Comments
Notes:
- The signature input length is the number of bytes which are used to generate the SHA-1 which is used to generate the ECDSA signature. The length should be eveything from the beginning until the signature itself. The decrypted version of the input data is used.
Metadata Section Headers
Struct
typedef struct {
uint64_t data_offset;
uint64_t data_size;
uint32_t type; // 1 = shdr, 2 = phdr, 3 = sceversion
uint32_t program_idx; // 0,1,2,3,etc for phdr, always 3 for shdrs, sceversion shdr number for sceversion
uint32_t hash_algorithm; // 2 = sha1_hmac, 3 = sha1
uint32_t hash_idx;
uint32_t enc_algorithm; // 1 = plain, 2 = aes128cbccfb, 3 = aes128ctr
uint32_t key_idx;
uint32_t iv_idx;
uint32_t compressed; // 1 = no; 2 = yes
} __attribute__((packed)) METADATA_SECTION_HEADER;
Comments
Notes:
- The metadata section headers are located after the metadata header in the SELF file.
- The number of sections is indicated by the sectionCount entry in the metadata header.
- They are decrypted using AES128CTR with the key and ivec entries from the metadata information.
- Section data is decrypted using AES128CTR with the key and ivec from the metadata keys specified by keyIndex and ivecIndex.
- Section data will also need to be uncompressed using zlib.
- The dataOffsets of the metadata section headers match in general the segment information dataOffsets.
- This is only present if the Metadata Header is present.
- Official name is segment_certification_header.
Section Hash
Struct
typedef struct {
uint8_t sha1[20];
uint8_t padding[12];
uint8_t hmac_key[64];
} __attribute__((packed)) SECTION_HASH;
Comments
Notes:
- The metadata keys (section hash) are located after the metadata section headers in the SELF file.
- The number of keys is indicated by the keyCount entry in the metadata header.
- They are decrypted using AES128CTR with the key and ivec entries from the metadata information.
- If the sha1Index points to a key, then key[sha1Index] and key[sha1Index+1] form the 160-bit hash. key[sha1Index+2] to key[key[sha1Index+6] form the 512-bit key for the HMAC-SHA1. The HMAC-SHA1 is calculated on the decrypted data and before the decompression.
Capabilities Info
Struct
typedef struct {
uint32_t type; // ex: 1, 2
uint32_t capabilities_size; // [[Capability Flags|capabilities]] Type 1: 0x30, Type 2: 0x100
uint32_t next; // 1 if there is another optional header structure after this, else 0
uint32_t unknown2;
uint64_t unknown3;
uint64_t unknown4;
uint64_t flags;
uint32_t unknown6;
uint32_t unknown7;
} __attribute__((packed)) CAPABILITIES_INFO;
Comments
Notes:
- This struct is some optional_header.
- It contains capability flags also known as encrypted_capability.
Signature
Struct
typedef struct {
uint8_t r[21];
uint8_t s[21];
uint8_t padding[6];
} __attribute__((packed)) SIGNATURE;
Comments
Notes:
- The signature is located after the the signature information in the SELF file.
- It is even present if the signature information is not present.
- It is decrypted using AES128CTR with the key and ivec entries from the Metadata Information.
Segment Extended Header
Temp name was SELF Section Info. Official name is segment_ext_header.
Struct
typedef struct {
void *data;
uint64_t size;
uint64_t offset;
} segment_ext_header;
Extracting an ELF
ELF Header
Elf64_Ehdr elfHeader; fseek ( selfFile, fix64 ( selfHeader.elfHeaderOffset ), SEEK_SET ); fread ( &elfHeader, sizeof ( Elf64_Ehdr ), 1, selfFile ); fseek ( elfFile, 0, SEEK_SET ); fwrite ( &elfHeader, sizeof ( Elf64_Ehdr ), 1, elfFile );
Section Headers
Elf64_Shdr elfSectionHeaders[100]; fseek ( selfFile, fix64 ( selfHeader.elfSectionHeadersOffset ), SEEK_SET ); fread ( elfSectionHeaders, sizeof ( Elf64_Shdr ), fix16 ( elfHeader.e_shnum ), selfFile ); fseek ( elfFile, fix64 ( elfHeader.e_shoff ), SEEK_SET ); fwrite ( elfSectionHeaders, sizeof ( Elf64_Shdr ), fix16 ( elfHeader.e_shnum ), elfFile );
Section Data
Notes:
- Unknown, manually copying the data over works for now.
- There should be a section data offset somewhere.
Program Headers
Elf64_Phdr elfProgramHeaders[100]; fseek ( selfFile, fix64 ( selfHeader.elfProgramHeadersOffset ), SEEK_SET ); fread ( elfProgramHeaders, sizeof ( Elf64_Phdr ), fix16 ( elfHeader.e_phnum ), selfFile ); fseek ( elfFile, fix64 ( elfHeader.e_phoff ), SEEK_SET ); fwrite ( elfProgramHeaders, sizeof ( Elf64_Phdr ), fix16 ( elfHeader.e_phnum ), elfFile );
Program Data
Notes:
- Load the metadata information and decrypt the key and ivec entries using AES256CBC using erk and riv.
- Load the metadata header and decrypt it using AES128CTR with the key and ivec entries from the metadata information.
- Load sectionCount metadata section headers and decrypt them using AES128CTR with the key and ivec entries from the metadata information.
- Load keyCount metadata keys and decrypt them using AES128CTR with the key and ivec entries from the metadata information.
- For each metadata section:
- In the SELF file, fseek to dataOffset and read in dataSize bytes.
- Decrypt the data using AES128CTR with the key and ivec from the metadata keys specified by keyIndex and ivecIndex from the metadata section header.
- Uncompress the data using zlib.
- Write it to the ELF file as the program section specified by section Index in the metadata section header.
Meta Checksums
There are 3 checksums at the offset specified by meta_offset.
- The first is the sha1 checksum of the entire self file.
- The 2nd checksum is the inverse of the first checksum.
- The 3rd checksum is the first checksum XORed with 0xAAAAAA..AAAAAB
The PSJailbreak payload ignores the actual checksums, but checks that the 3rd checksum is the 2nd checksum XORed with 0xAAAAAA..AAAAAB
Capabilities Flags
appldr
0x17 = 0x78
xsetting
0x17 = 0x3B 0x1B = 0x01 0x1D = 0x02
ps3swu
0x17 = 0x7B 0x1B = 0x01 0x1D = 0x11 0x1E = 0x60
lv2
0x17 = 0x7B 0x1B = 0x01
lv1
0x17 = 0x7B 0x1B = 0x01
libfs
0x17 = 0x7B 0x1B = 0x01
icolaunch
0x17 = 0x3B 0x1B = 0x01 0x1D = 0x04
hddcopy
0x17 = 0x7B 0x1B = 0x01 0x1D = 0x08
flowers
0x17 = 0x3B 0x1B = 0x01 0x1E = 0x20
fdm_spu
0x17 = 0x38
emu_drm
0x17 = 0x3B 0x1D = 0x02
bdj
0x0F = 0x01 //qa-bdp type1 0x17 = 0x27 0x1D = 0x02
swagner
0x0F = 0x02 //qa-bdp type2 0x17 = 0x3F 0x1D = 0x02
0x0C = 0x00000001 / 0x00000002 // qa_bdp_type_flags
0x14 = 0x00000038 / 0x0000003B / 0x00000078 / 0x0000007B / 0x00000027
0x18 = 0x00000001
0x1C = 0x00002000 / 0x00020000 / 0x00040000 / 0x00080000 / 0x00116000
0x14:
#define CAP_FLAG_REFTOOL 0x08 // DEH #define CAP_FLAG_DEBUG 0x10 // DEX #define CAP_FLAG_RETAIL 0x20 // CEX #define CAP_FLAG_SYSDBG 0x40 // ARCADE
Some more cap flags: http://pastie.org/3090973 and http://pastie.org/3090976 (appldr 356 white(?)list) abbr title="ECDSA - Elliptic Curve Digital Signature Algorithm">ECDSA
| |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||